When UIDAI came up with Aadhaar card, people thought it would make a significant impact in the lives of the people. As government made it compulsory to link the card with multiple services, it has literally become a part of the lives in India.
The authorities introduced a mobile application named mAadhaar to conveniently carry the Aadhaar card information. The user has to set a password first and enter the same every time he/she wants to see the details.
A French Security Expert Exposes the Vulnerability of mAadhaar Application
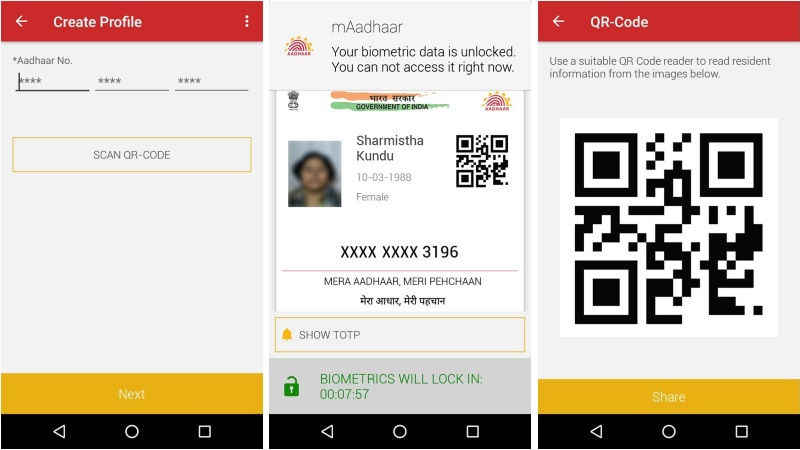
You might have already installed mAadhaar application on your phone to reduce the size of your wallet. It helps you have the card right on the phone screen.
Earlier, a French security expert named Robert Baptiste who appears as Elliot Alderson on Twitter showed the mAadhaar app is insecure. He even demonstrated how easy it is to crack into the source code of the application.
At the time he shared the issue, the app was saving the biometric settings in a local database with password protection. The most concerned fact is the way the app generated the password. The developers had used the 3 digits random number along with the string db_password_123.
So, the issue became public, and UIDAI didn’t bother to update the app. At a point, the tech world thought they lost the release key as well. Despite the speculations, the authorities managed to update the application.
Well, it hasn’t become secure yet. Alderson published another video on Twitter depicting the method to bypass the password without racking the brain. For the method to work, the attacker should have the physical access to the victim’s phone.
The official Twitter handle of Aadhaar responded to the issue saying Aadhar details are not confidential. All they consider private is the biometric details. However, it leads to a major security breach. They are silently admitting that it is possible to surpass the password protection of the application. When someone does and gets access to the details, it is not going to be harmful, they say.
You know how demographic data like Aadhaar, PAN, address, phone number, and emails are exploited. People can get into the official websites and attempt to reset a confidential password using such details. In the world of dark web, getting the password to an email or fraudulently achieving (either by duplicating the SIM or by fake phone calls) the OTP sent to a number isn’t as hard as it may seem.
We are not saying it will cause a major outage. Still, there is a chance for fraudsters to even transfer the funds from your bank account (there are Aadhaar based payment platforms).